Seal/Unseal
When an OpenBao server is started, it starts in a sealed state. In this state, OpenBao is configured to know where and how to access the physical storage, but doesn't know how to decrypt any of it.
Unsealing is the process of obtaining the plaintext root key necessary to read the decryption key to decrypt the data, allowing access to the OpenBao.
Prior to unsealing, almost no operations are possible with OpenBao. For example authentication, managing the mount tables, etc. are all not possible. The only possible operations are to unseal the OpenBao and check the status of the seal.
Why?
The data stored by OpenBao is encrypted. OpenBao needs the encryption key in order to decrypt the data. The encryption key is also stored with the data (in the keyring), but encrypted with another encryption key known as the root key.
Therefore, to decrypt the data, OpenBao must decrypt the encryption key which requires the root key. Unsealing is the process of getting access to this root key. The root key is stored alongside all other OpenBao data, but is encrypted by yet another mechanism: the unseal key.
To recap: most OpenBao data is encrypted using the encryption key in the keyring; the keyring is encrypted by the root key; and the root key is encrypted by the unseal key.
Shamir seals
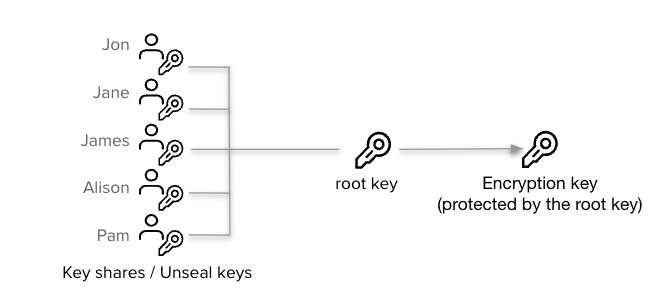
The default OpenBao config uses a Shamir seal. Instead of distributing the unseal key as a single key to an operator, OpenBao uses an algorithm known as Shamir's Secret Sharing to split the key into shares. A certain threshold of shares is required to reconstruct the unseal key, which is then used to decrypt the root key.
This is the unseal process: the shares are added one at a time (in any order) until enough shares are present to reconstruct the key and decrypt the root key.
Unsealing
The unseal process is done by running bao operator unseal or via the API.
This process is stateful: each key can be entered via multiple mechanisms from
multiple client machines and it will work. This allows each share of the root
key to be on a distinct client machine for better security.
Note that when using the Shamir seal with multiple nodes, each node must be unsealed with the required threshold of shares. Partial unsealing of each node is not distributed across the cluster.
Once an OpenBao node is unsealed, it remains unsealed until one of these things happens:
-
It is resealed via the API (see below).
-
The server is restarted.
-
OpenBao's storage layer encounters an unrecoverable error.
Note: Unsealing makes the process of automating an OpenBao install difficult. Automated tools can easily install, configure, and start OpenBao, but unsealing it using Shamir is a very manual process. For most users Auto Unseal will provide a better experience.
Sealing
There is also an API to seal the OpenBao. This will throw away the root key in memory and require another unseal process to restore it. Sealing only requires a single operator with root privileges.
This way, if there is a detected intrusion, the OpenBao data can be locked quickly to try to minimize damages. It can't be accessed again without access to the root key shares.
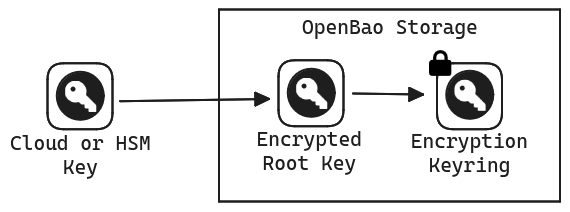
Auto unseal
Auto Unseal was developed to aid in reducing the operational complexity of keeping the unseal key secure. This feature delegates the responsibility of securing the unseal key from users to a trusted device or service. At startup OpenBao will connect to the device or service implementing the seal and ask it to decrypt the root key OpenBao read from storage.
There are certain operations in OpenBao besides unsealing that require a quorum of users to perform, e.g. generating a root token. When using a Shamir seal the unseal keys must be provided to authorize these operations. When using Auto Unseal these operations require recovery keys instead.
Just as the initialization process with a Shamir seal yields unseal keys, initializing with an Auto Unseal yields recovery keys.
It is still possible to seal an OpenBao node using the API. In this case OpenBao will remain sealed until restarted, or the unseal API is used, which with Auto Unseal requires the recovery key fragments instead of the unseal key fragments that would be provided with Shamir. The process remains the same.
For a list of examples and supported providers, please see the seal documentation.
Warning: Recovery keys cannot decrypt the root key, and thus are not sufficient to unseal OpenBao if the Auto Unseal mechanism isn't working. They are purely an authorization mechanism. Using Auto Unseal creates a strict OpenBao lifecycle dependency on the underlying seal mechanism. This means that if the seal mechanism (such as the Cloud KMS key) becomes unavailable, or deleted before the seal is migrated, then there is no ability to recover access to the OpenBao cluster until the mechanism is available again. If the seal mechanism or its keys are permanently deleted, then the OpenBao cluster cannot be recovered, even from backups. To mitigate this risk, we recommend careful controls around management of the seal mechanism, for example using AWS Service Control Policies or similar.
Recovery key
When OpenBao is initialized while using an HSM or KMS, rather than unseal keys being returned to the operator, recovery keys are returned. These are generated from an internal recovery key that is split via Shamir's Secret Sharing, similar to OpenBao's treatment of unseal keys when running without an HSM or KMS.
Details about initialization and rotation follow. When performing an operation
that uses recovery keys, such as generate-root, selection of the recovery
keys for this purpose, rather than the barrier unseal keys, is automatic.
Initialization
When initializing, the split is performed according to the following CLI flags and their API equivalents in the /sys/init endpoint:
recovery-shares: The number of shares into which to split the recovery key. This value is equivalent to therecovery_sharesvalue in the API endpoint.recovery-threshold: The threshold of shares required to reconstruct the recovery key. This value is equivalent to therecovery_thresholdvalue in the API endpoint.recovery-pgp-keys: The PGP keys to use to encrypt the returned recovery key shares. This value is equivalent to therecovery_pgp_keysvalue in the API endpoint, although as withpgp_keysthe object in the API endpoint is an array, not a string.
Additionally, OpenBao will refuse to initialize if the option has not been set to generate a key, and no key is found.
Rotation
Unseal key
OpenBao's unseal key can be rotated using a normal bao operator rotate-keys
operation from the CLI or the matching API calls. The rotation is authorized
by meeting the threshold of recovery keys. After rotation, the new barrier
key is wrapped by the HSM or KMS and stored like the previous key; it is not
returned to the users that submitted their recovery keys.
Recovery key
The recovery key can be rotated to change the number of shares/threshold or to
target different key holders via different PGP keys. When using the OpenBao CLI,
this is performed by using the -target=recovery flag to bao operator rotate-keys.
Via the API, the rotation is performed using
/sys/rotate/recovery endpoint.
Seal migration
The Seal migration process cannot be performed without downtime, and due to the technical underpinnings of the seal implementations, the process requires that you briefly take the whole cluster down. While experiencing some downtime may be unavoidable, we believe that switching seals is a rare event and that the inconvenience of the downtime is an acceptable trade-off.
NOTE: A backup should be taken before starting seal migration in case something goes wrong.
NOTE: Seal migration operation will require both old and new seals to be available during the migration. For example, migration from Auto Unseal to Shamir seal will require that the service backing the Auto Unseal is accessible during the migration.
NOTE: Seal migration from Auto Unseal to Auto Unseal of the same type is supported in OpenBao. However, there is a current limitation that prevents migrating from AWSKMS to AWSKMS; all other seal migrations of the same type are supported. Seal migration from One Auto Unseal type (AWS KMS) to different Auto Unseal type (HSM, Azure KMS, etc.) is also supported on older versions as well.
Migration steps
These steps are common for seal migrations between any supported kinds and for any storage backend.
-
Take a standby node down and update the seal configuration.
- If the migration is from Shamir seal to Auto seal, add the desired new Auto seal block to the configuration.
- If the migration is from Auto seal to Shamir seal, add
disabled = "true"to the old seal block. - If the migration is from Auto seal to another Auto seal, add
disabled = "true"to the old seal block and add the desired new Auto seal block.
Now, bring the standby node back up and run the unseal command on each key, by supplying the
-migrateflag.- Supply Shamir unseal keys if the old seal was Shamir, which will be migrated as the recovery keys for the Auto seal.
- Supply recovery keys if the old seal is one of Auto seals, which will be migrated as the recovery keys of the new Auto seal, or as Shamir unseal keys if the new seal is Shamir.
-
Perform step 1 for all the standby nodes, one at a time. It is necessary to bring back the downed standby node before moving on to the other standby nodes, specifically when Integrated Storage is in use for it helps to retain the quorum.
-
Step down the active node. One of the standby nodes will become the new active node. When using Integrated Storage, ensure that quorum is reached and a leader is elected.
-
The new active node will perform the migration. Monitor the server log in the active node to witness the completion of the seal migration process. Wait for a little while for the migration information to replicate to all the nodes in case of Integrated Storage.
-
Seal migration is now completed. Take down the old active node, update its configuration to use the new seal blocks (completely unaware of the old seal type) ,and bring it back up. It will be auto-unsealed if the new seal is one of the Auto seals, or will require unseal keys if the new seal is Shamir.
-
At this point, configuration files of all the nodes can be updated to only have the new seal information. Standby nodes can be restarted right away and the active node can be restarted upon a leadership change.